Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
I got to attend BSides MCR for the first time this year, and it was well worth it.
I apologize for the pun in the title, but Manchester definitely tries to put the bee in BSides.
This was actually not my first time in Manchester, but it was nice visiting there again.
I ended up making a longer trip of this con, so that I would have some time to myself.
First, I walked around the city for a bit and got over my jet-lag the first few days in town.
The day after the con, I got to take a tour of Old Trafford stadium, which was incredible.
Afterwards, I headed back to the neighborhood around my hotel and had some Pancho’s Burritos. The food was awesome, and I’m glad for the recommendation.
Finally, I spent one night drinking at the hotel bar with a local, which was also pretty fun.
BeerSides was the night before at a pub a block from my hotel, and it was a great start.
There were a handful of lightning talks, and more than a handful of people there.
It was an awesome experience to actually meet members of a community that I knew none of.
I had a few beers, had a few laughs, met a lot of people, and really enjoyed myself. By the end of BeerSides alone, I knew I wanted to come back to BSides MCR.
I was only able to make it to a few talks, but they were still awesome.
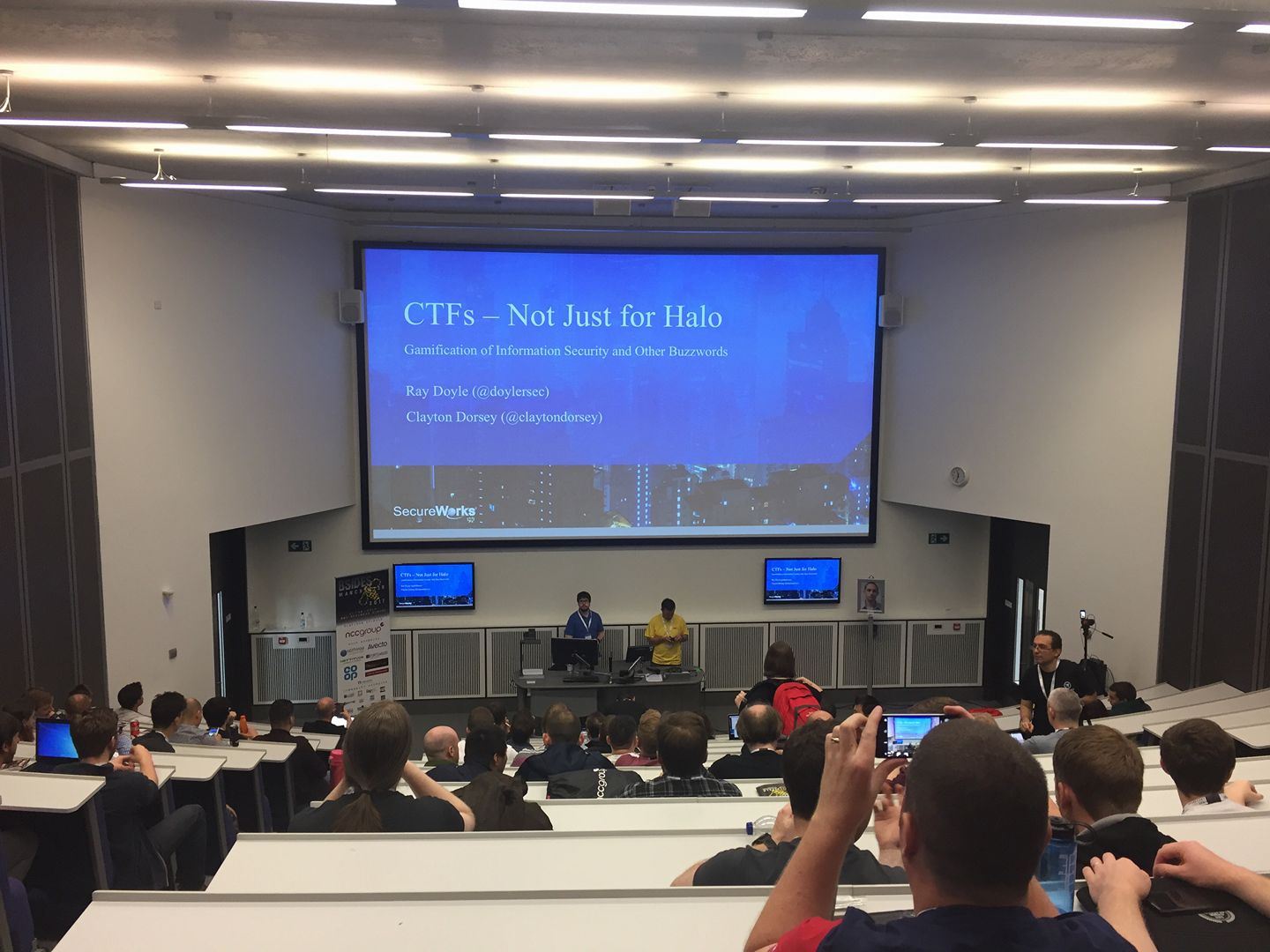
It was an honor speaking at BSides MCR 2017, and I’m so glad that they invited me.
The presentation went great, and I wish Clayton could have made it. The crowd was awesome, and I had people coming up to me throughout the con regarding it.
While this talk went a bit better than the last one, I did still forget a few things. Other than my speed, I think it was still a great experience.
I might not give this talk at another con (stay tuned), so it’s time to start on next year’s!
The resource page can always be found here, and feel free to offer additions.
As always, if you have any feedback (positive, negative, or neutral) about the content or speaker, then it’s always welcome.
It’s not a con if I don’t spend some time participating in a CTF, and this was no different.
Eric and I ended up competing, and winning, in the NCC Group CTF. We of course competed with the tongue in cheek name of, “SC > NCC”. Note that the testing123 account was theirs to test things.
This was a shorter CTF, with only 8 challenges. Two were VERY basic web, and the third web was some fairly simple SQL injection.
The other 5 challenges were all based around escaping a restricted shell or environment. It was definitely a fun, albeit difficult, CTF to compete in. We ended up winning with 2/5 of the escapes solved, and the 2nd place team only had 1/5.
In the end, we ended up winning a DIY 3D printer that I had to get back to America.
While I have not put it together yet, you can always follow it on Twitter @BsidesMCRPrint
First, huge thanks to the BSides MCR crew for putting on a great con, and for allowing me to speak at it.
This is a con that I’d love to go to in the future, if I have the chance. If you are local to the area, and interested in security, then you can’t miss it.
Finally, I got to witness the most American burger at the con after-party. It was [a patty, cheese, bacon, and a fried chicken breast] x2. While this cannot compare, here is a picture of MY burger (just one set of those toppings with pulled pork on top).
Ray Doyle is an avid pentester/security enthusiast/beer connoisseur who has worked in IT for almost 16 years now. From building machines and the software on them, to breaking into them and tearing it all down; he’s done it all. To show for it, he has obtained an OSCE, OSCP, eCPPT, GXPN, eWPT, eWPTX, SLAE, eMAPT, Security+, ICAgile CP, ITIL v3 Foundation, and even a sabermetrics certification!
He currently serves as a Senior Staff Adversarial Engineer for Avalara, and his previous position was a Principal Penetration Testing Consultant for Secureworks.
This page contains links to products that I may receive compensation from at no additional cost to you. View my Affiliate Disclosure page here. As an Amazon Associate, I earn from qualifying purchases.
[…] (Speaker) BSides MCR 2017 was an UnBEElievable Time […]