Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Some time ago I setup my pfSense DNSBL, and I wanted to share my configuration and results.
A DNSBL is a list of domains that the application/network does not properly resolve, hence the “black-hole”.
Originally, DNSBLs prevented spam e-mails from reaching users.
In this case, I wanted to block as many ads, malvertising, etc. as possible.
If you prefer a video over reading the text, then you can find the YouTube version of this post below.
That said, don’t forget to hit those like and subscribe buttons to help support the blog and channel!
To start, I installed the pfBlockerNG package by going to System -> Package Manager -> Available Packages. To quote their description, “pfBlockerNG is the Next Generation of pfBlocker. Manage IPv4/v6 List Sources into ‘Deny, Permit or Match’ formats.”
Once I installed the plugin, I was able to configure it by going to Firewall -> pfBlockerNG.
I enabled the blocker, told the settings to persist, and set the CRON job to run every 3 hours.
After I enabled the blocker, I clicked on DNSBL to configure my block list.
I enabled DNSBL, set my Virtual IP to 10.10.10.1, and kept my listening ports and interface default.
With the basic settings in place, it was time to set up my actual block list!
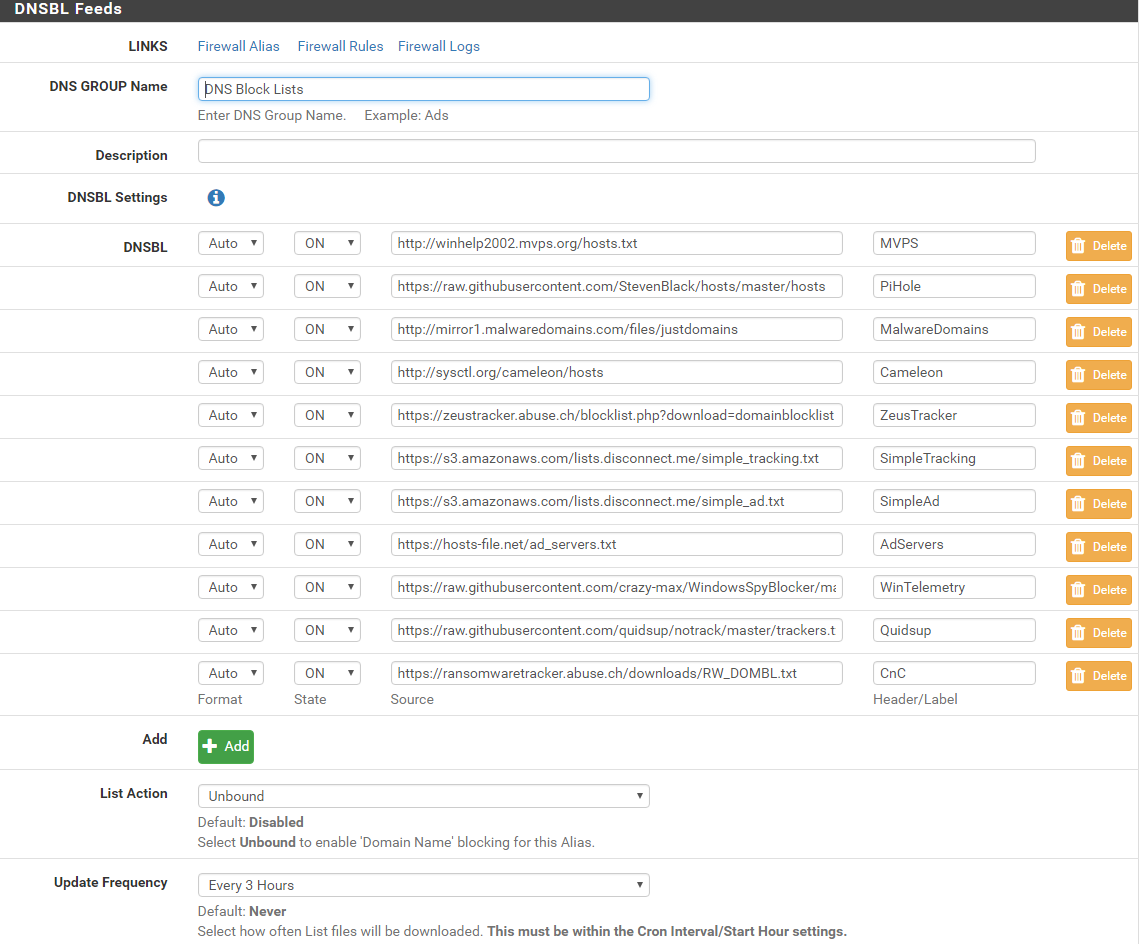
Selecting the DNSBL Feeds menu option and clicking “Add” allowed me to create a new DNS Group with any number of block list feeds.
I started with a number of lists from the Pi-hole ad block list.
NOTE: Do not put a link to the Pi-hole ad block list directly, but rather to each individual entry. If you do this (trust me, I did at first), then you will only block your access to the actual block list feeds in question. To fix this you will need to remove the block, clear the feeds, clear the caches, and possibly restart your router.
Once I had my feeds selected, I added them to my new DNS Group.
To test my feeds, I tried to visit an advertising site directly, and the router blocked my DNS request!
As a bonus, I also setup ntopng for some basic visualization.
Per their package description, “ntopng (replaces ntop) is a network probe that shows network usage in a way similar to what top does for processes.”
Once I installed the package, I was able to configure it by going to Diagnostics -> ntopng Settings.
I enabled the plugin, told my settings to persist, changed the default admin password, and configured it for my LAN.
After the plugin was running, I logged in and took a look at my Talkers flow.
This was pretty neat to watch, but not anything that I see myself using for now.
Additionally, the interface chart was cool to see how much bandwidth my network was using, and when.
Ray Doyle is an avid pentester/security enthusiast/beer connoisseur who has worked in IT for almost 16 years now. From building machines and the software on them, to breaking into them and tearing it all down; he’s done it all. To show for it, he has obtained an OSCE, OSCP, eCPPT, GXPN, eWPT, eWPTX, SLAE, eMAPT, Security+, ICAgile CP, ITIL v3 Foundation, and even a sabermetrics certification!
He currently serves as a Senior Staff Adversarial Engineer for Avalara, and his previous position was a Principal Penetration Testing Consultant for Secureworks.
This page contains links to products that I may receive compensation from at no additional cost to you. View my Affiliate Disclosure page here. As an Amazon Associate, I earn from qualifying purchases.
Hey Doyler, great post. Will have to check this out. Your PFSense is deployed at home? If so, is your hardware a PC or did you actually purchase the PFSense firewall?
Thanks, it is definitely nice (especially for sites that ABP doesn’t catch or that make me disable it).
Yes, deployed at home and what I use for my routing now.
It’s a white-box build that I did myself actually. See this post here for the build info – https://www.doyler.net/security-not-included/zotac-zbox-ci323-pfsense
Stupid question but did you have to point your internal systems to the pfsense box as it’s DNS resolver? Do you need change your DNSBL from “disabled” to “unbound”? Do I need to enable and configure unbound as a forwarder or resolver of some sort?
Not stupid, and glad to help. Since pfSense was already my router and providing DHCP, my internal systems were already pointing to it for DNS resolution. That said, I do have DNS resolver (not Forwarder) enabled so that it can actually perform the resolution and use the DNSBL. You will need to enable and configure Unbound (this is just the name of DNS Resolver in Services -> DNS Resolver). Most of my settings are default though, so it isn’t much extra work.
hi mate im wondering if you could help me cant seem to get it to block anything
is there any chance you could add me on skype joshhopey would be great if you could
Hi Josh,
It won’t block anything by default, but you will need to subscribe to some feeds. Have you done that yet?
Hey Doyler, great write up! I’m new to pfSense so I’m a bit confused. I have Google set as my DNS Server. Should I leave that blank for my ads to be blocked or can I still use 8.8.8.8 and my ads will be blocked on my mobile devices?
Hi Joel,
Thanks, and glad to help! You will need to use the DHCP provided DNS server (your pfSense box – 192.168.1.1) on all of your internal devices.
Then, if you want to continue to use Google as your outbound DNS server, then you can set that under System -> General Setup
Heads up, pfblocker now supports domain blacklists for web filtering purposes, including support for Squidblacklist.org subscribers.
We are a subscription based service, gotta pay the bills, but we do have some free stuff for the community as well, so come on over and check it out.
Interesting, thanks for that.
Not sure if I’ll subscribe since I tend to build my own or use free blacklists, but others here may want to!
How can I just deploy on Vultr vps
I gonna use vpn service to block
Is it posibble?
Thanks
While you could deploy your own DNS server on Vultr, it defeats the point by then.
First, you should only really be using a VPN service when you have to.
That said, VPN isn’t really for ad blocking in particular, so it depends on what you’re hoping to achieve. If you do setup your own VPN service, you could setup a DNSBL of your own though.
Hi There. Just got my first pfSense device today – a HP thinclient pre-loaded with pfSense 2.3.3. Super excited. Followed your instructions, DNSBL enabled, DNSBL Feeds contain a Group I created with most of the feeds you have shown. However, once enabled, (Update & Cron ran), upon testing with ‘usemax.de’, I’m not seeing it being blocked. Able to reach it just fine. What am I missing?
Awesome, great to hear! Hmm, there are a few possibilities. First, are you sure that that site is on one of the feeds you selected? If not, try to select a different URL that you know is on the list. Other than that, are you using your pfSense box as a DNS resolver for your client, or still hitting your ISP/Google directly?
Hi doyler great guide, i was wondering if you know how to white list a site when using DNSBL I am able to white list stuff when just using pfblockerng but not when using the lists with DNSBL any help with this would be great.
I must say it again GREAT guide!!
Hi Aidan,
I’m glad you enjoyed the guide, and happy it helped!
Great question, and I’ve run into that issue plenty. If you go to Firewall -> pfBlockerNG -> DNSBL you will be on the right page.
From there, go down to “Custom Domain Whitelist” and add your sites. Note that this field doesn’t support regex, so you will need to be specific.
Worked perfectly and loved the quick reply :-)….
Any chance you know how to block YouTube ads? Even if you know a method that doesn’t involve pfsense I would be glad to hear any tips I could Google and work out for myself. I have tried a few things with pi-hole in the past but could never get anything working.
In theory you might be able to block *.googlevideo.com, but I have never tried it myself.
That said, I’m not sure if I’m even getting ads on YouTube currently, but I’ll try to pay more attention.
Sorry for doing your head in, but I have tried a few things now to get the amazon shopping app for android to work any chance you have any idea what to whitelist to get it working?
Also I found a list that blocks YouTube ads. In case anyone else wants to block YouTube ads just ad this to the DNSBL feeds
https://raw.githubusercontent.com/kbinani/adblock-youtube-ads/master/signed.txt
It worked for me
No problem, and glad to help.
I forget exactly what you need to unblock since I normally just use the web version. That said, the easiest thing to do in this case is to go to the logs and view the dnsbl.log file. This will show you what was blocked most recently, and you can start white-listing via that!
Awesome, thanks, I’ll have to give it a try if they aren’t already there.
good morning
is possible add category also form shalla or ut1 ?
thanks Alberto
Hi Alberto,
What sort of categories are you trying to add?
Okay I just wanted to throw this out there. Here is a collection of lists that are well vetted and up to date. https://isc.sans.edu/suspicious_domains.html
Awesome, thanks for that!
I’ll probably have to take a look and replace some/all of my lists with that.
I cannot get pfBlockerNG to work. First I loaded a page while using pi-hole in its own browser tab. I then changed DNS from pi-hole to my pfsense server and then opened the same page in a new tab.
pi-hole pages has blank areas where ads would have been
pfBlockerNG has the original ads.
I added the lists from pi-hole “adlists.default” to pfBlockerNG one by one , and then force updated. I watched the update log go through each list and load it, then it restarted Unbound.
As far as I can tell , everything is enabled.
pfBlockerNG is enabled
DNSBL is enabled
DNS Resolver is enabled ( and working )
*** note that my DSN Resolver has this option checked “DNS Query Forwarding Enable Forwarding Mode” is this the problem?
Nm, that was the problem! I’m on Day 2 of using pfSense and I’m finding that it’s a great investment of my time. For the record I’m running it on the Netgate SG-3100 with pfsense 2.4.1 .
Sorry for the late reply, back to back on-site engagements for clients!
Great, I’m glad you figured out the problem and that it is now working for you. Did you pickup the Netgate from eBay, or somewhere else? How are you liking running it on that device?
Thanks for taking the time to build this blog post dude. I’ve got DNSBL on my pfSense running now.
You’re welcome, and awesome! Let me know if you run across any questions, issues, or suggestions.
I never got this thing working after spending two full days on it. It doesn’t play nicely with OpenVPN. The two modules basically hate each other. AdGuard actually works better anyway as it attempts to fix the formatting of the page after it removes the ads.
In fact, I actually gave up using pf sense as a system-wide filter. My house is full of wifi tech including the lighting, fans, audio, televisions, security, locks, thermostat and Echo Dots for voice control. Throwing pfSense into the mix was disastrous. Every time I got close to fixing one thing, two other things would break. LOL. I almost jumped off the balcony. I finally pulled the pfSense box out of the main line and put it where it needed to be–the wired units that are exposed and cannot protect themselves well, namely the TV streaming systems. Sure, the computer needs a firewall, but running it locally means I can turn it off when it is not working properly.
I haven’t actually tried with OpenVPN, but it should work just fine out of the box. Never used AdGuard, but that sounds like a nice feature at least.
Haha, IOT devices are one of the reasons that I WANTED DNSBL/pfSense (blocking all of the garbage that they are sending back). That seems like a reasonable setup though, and glad it works!
I’m having an issue with a website where the comment section is not loading. If you have pfblocker active go to politico.com and try to load the comment section of every article and you will see that it will not work.
Ads are being blocked fine but i just need the comments section to load properly
Any help is appreciated
Hi!
You are likely experiencing this issue due to something (possibly ads or a 3rd party library) being blocked by pfBlocker.
I am away from my pfSense installation for a bit, but I will try to walk you through the steps for troubleshooting and fixing this issue. I’ve run into it on a few sites, and it is normally not too bad to fix.
In this case, what I normally do is go to the pfBlocker -> dnsbl.log file under “Logs”. Once you see what is being blocked on that page that is important, you can add that domain (no wildcard) to your pfBlocker Whitelist (towards the bottom of the settings page).
Once you do that, you can reload your lists under “Sync” and the page should work just fine. If that doesn’t work or help, then I’ll gladly post a tutorial on it once I get back!
Im whitelisting the website completely and still it is being blocked by dnsbl. Please do post a tutorial on how to whitelist domains properly to help fix broken websites. Thanks for your help.
Understandable. Once I get home I will gladly post a tutorial about what might be happening and how to whitelist to fix that issue!
And it’s posted!
https://www.doyler.net/security-not-included/pfsense-dnsbl-whitelisting
“Enable TLD (BETA)”
trigger this on may helps domain based DNS block.
Ex:
facebook.com
blocks facebook.com, http://www.facebook.com, jp.facebook.com, tw.facebook.com
Thanks for your share, really helps!
Definitely an option, but can also cause some speed/performance issues. That, and I don’t want to mess with more white-listing than I need to!
Thanks, and glad to help.
I have followed your instructions and I’m unable to get to certain sites. Where do I check to see if I’m being blocked by one of the lists?
Hi Glen,
If some sites are being blocked, then you can check out my tutorial on that as well!
https://www.doyler.net/security-not-included/pfsense-dnsbl-whitelisting
Im a bit late to the party, but put you browser into development mode (F12 in chrome). Then load the webapage. Now look at the network tab. You should be able to find what is not working in there as it will appear red. From there you can look at whitelisting the component,
Yup, definitely!
I added an additional post about whitelisting for people with issues – https://www.doyler.net/security-not-included/pfsense-dnsbl-whitelisting
[…] 6 Comments / Security Not Included / By Ray Doyle / March 17, 2018 March 5, 2021 […]