Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Today I want to cover what exactly multi factor authentication or two-factor authentication is, what any abbreviations (like MFA or 2FA) are, and how you SHOULD be using it to protect yourself!
Two Factor Authentication (2FA), is an additional level of authentication used to ensure the security of accounts in addition to a standard username and password. The benefit of authentication should be obvious, but it prevents others from pretending to be us, and potentially stealing money or valuable information from private resources.
Before I can jump into MULTI-factor authentication, I’ll first have to cover what exactly authentication means in the realm of information security.
According to NIST, authentication is “verifying the identity of a user, process, or device, often as a prerequisite to allowing access to resources in an information system.”
In simpler terms, authentication is how you prove to a system that you are who you say you are. Whenever you log in to your social media accounts, your banking applications, or even your work computers, you are authenticating!
Normally, authentication takes two steps: first, you identify who you are (for example your username or e-mail address), then you PROVE that you are who you say you are (for example a password that only you know).
Get Your NordVPN Offer Now!There are three primary methods of authentication: something you are (for example biometrics like a fingerprint scanner), something that have (for example a token on your keychain or an app like the Google authenticator), or something you know (for example passwords).
In addition to these, some systems may also use somewhere you are (for example GPS location on your phone) or some “time” you are (for example: if you normally only log in to your bank between the hours of 9 am and 5 pm EST). That said, these are generally not enough authentication factors on their own, so systems normally use these in conjunction with one of the other methods.
Something you are is USUALLY the strongest form of authentication, because, as you’d expect, it’s pretty hard to duplicate an iris or copy a fingerprint. That said, the TECHNOLOGY behind some of these authentication methods can be expensive, and cheaper versions may have implementation flaws of their own. This authentication method is starting to become more common (for example the iPhone Face ID), but this is still too expensive to be common in every system that we use.
Something you have has been increasing in popularity over the last few years, especially with the explosion of the smartphone. This authentication method normally comes in the form of a one-time use token or key that comes from either an application you have (for example the Google Authenticator), a physical token that you carry around (for example an RSA token), or something like a text message/e-mail message. While this is another secure method of authentication, getting users a physical device proved to be a barrier before the smart device becoming universal.
Finally, the most common method of authentication is something you know. The primary example of this is passwords. There is no special hardware needed for biometrics, no apps for you to install, and no other tools required to provide our secrets. This is the reason that this is both the most common method of authentication, but ALSO the reason that this is the least secure method of authentication. Due to this, it is incredibly important that you not only create strong passwords, but you keep them as secure as possible.
Regardless of what method(s) of authentication you use, you should keep them all as secure as possible.
If someone were to know your username and password, for example, they could log in to your banking application and transfer out all of your money. Not only would you be out your money, but it could also be hard to prove that this wasn’t you because you “proved” to be yourself to the bank via your authentication mechanisms.
This means that you should keep any applications or tokens on your person or locked up, and you should uniquely generate any passwords and either store them nowhere or in a secure password vault.
In addition to passwords, this also covers answers to your “secret questions”, as these are effectively another method of “something you know” to most applications or services. If you are familiar with password reset mechanisms, you can normally change an account’s password just by answering a few of these “secret questions”.
Get Your NordVPN Offer Now!Finally, on to the core topic of what is multi-factor or two-factor authentication!
Multi-factor authentication, as some of you may have already guessed, is combining two (or more) authentication methods to provide greater security and identity verification. The form of this that you may be most familiar with is a password (something you know) + a one-time use token from your authenticator app (something you have).
Continuing with the banking example from earlier, if someone knew your username and password, they would STILL need to be able to access the one-time-use token from the application on your physical phone.
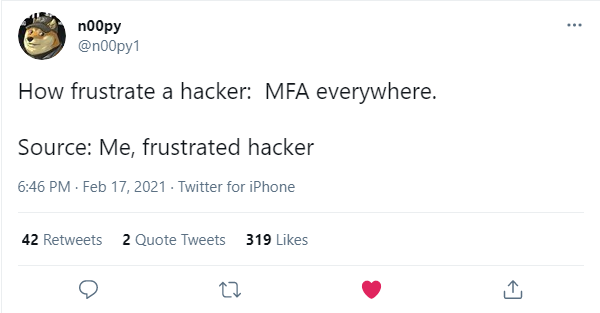
Multi-factor authentication is a huge benefit to security, and honestly the biggest thing that stops hackers LIKE ME from breaking into your company or private applications. While important, attackers can easily guess usernames and passwords, systems can leak them, or users can reuse them across multiple applications and services. By requiring an additional form of authentication, application owners can have increased confidence that users and services will be safer from attackers.
While people use MFA (multi-factor authentication) and 2FA (two-factor authentication) interchangeably, they aren’t exactly the same.
2FA is ONLY using two factors of authentication (for example the password and authenticator app from before).
Multi-factor authentication is two OR MORE factors of authentication (for example a password, an RSA keyring, the time that you normally log in to applications, and the GPS coordinates of your phone).
Get Your NordVPN Offer Now!While enabling multi-factor authentication will vary from system to system and application to application, I’ll give you a few examples to get yourself started!
For your Facebook account, you will want to log in, go to your “Security and Login Settings”, scroll down to “Use two-factor authentication” and click “Edit”.
While these are only two specific examples, hopefully, they give you an idea of where you might find these settings in the specific applications that you would like to enable them.
That said, if you cannot find this functionality, be sure to reach out to your system administrator or customer support and ask them about multi-factor authentication!
Hopefully, all of the above examples gave you plenty of reasons to enable multi-factor authentication everywhere.
The biggest takeaway should be that two-factor or multi-factor authentication is often the BIGGEST frustration to hackers everywhere. It is also the easiest step that you can take in protecting your accounts.
Ray Doyle is an avid pentester/security enthusiast/beer connoisseur who has worked in IT for almost 16 years now. From building machines and the software on them, to breaking into them and tearing it all down; he’s done it all. To show for it, he has obtained an OSCE, OSCP, eCPPT, GXPN, eWPT, eWPTX, SLAE, eMAPT, Security+, ICAgile CP, ITIL v3 Foundation, and even a sabermetrics certification!
He currently serves as a Senior Staff Adversarial Engineer for Avalara, and his previous position was a Principal Penetration Testing Consultant for Secureworks.
This page contains links to products that I may receive compensation from at no additional cost to you. View my Affiliate Disclosure page here. As an Amazon Associate, I earn from qualifying purchases.
Hi
Thanks for this blog. It is very informative and provides a complete understanding of Two-factor authentication in detail.
You’re welcome, and hopefully it helped!