Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
I wanted to update and combine some of my hacker conference posts, so BSidesRDU made for a great first run at it!
While I may be biased, I have to say that BSidesRDU is the best hacker conference, at least in the Triangle. It’s run by a great local crew, and always has a ton of fun events (including EverSec CTF) and talks (often including me).
I’ve been going to BSidesRDU since it was BSides Raleigh back in 2016, and I wish I had started going sooner.
I’ve also managed to win a TON of prizes from Hacker Jeopardy and the CTF, so those don’t hurt either.
Get Your NordVPN Offer Now!I finally attended BSides Raleigh this past Thursday, and it was well worth it.
For those of you who have never been, this is a great conference for the price.
I didn’t attend any talks, but I was originally scheduled to give one! This would have been my first conference presentation, but it got pulled by my job at the last minute. Stay on the lookout for the slides and some additional information here in the future though.
The vendor area was spread out and open, and everyone there was quite friendly. There was also a provided lunch, and even beer later on in the evening.
I spent almost all of my time doing the CTF, and it was a fun one. EverSec ran the CTF this year, which was great. EverSec consists of a few of the people on the CTF team that I’m on, but I didn’t help them with this competition at all (so that I could compete).
The EverSec CTF operated in a mixed/scenario format, similarly to the DerbyCon CTF. A company got “hacked” and needed us to help find out additional information for them.
To start, there was a “Consultants” page with some forensics, steganography, and crypto challenges.
The network consisted of multiple machines with various vulnerabilities that could be compromised in addition to those challenges.
I enjoyed this CTF, and it was a unique experience. I had plenty to show for all of my time during it as well, as I ended up on top of the scoreboard!
As my prize for the CTF, I got a WiFi Pineapple Nano, which is awesome for a $20 con. I’m looking forward to playing with this and some new blog posts revolving around it.
Towards the end of the CTF, Veracode ran a round of Hacker Jeopardy. This was a fun competition, and not vendor-heavy (other than the bonus Final Jeopardy question, but that’s fine). I ended up getting 2nd in this as well, taking home a $25 Amazon Gift card.
The only other item of note from the con was the coolest speaker gift ever. I didn’t give my talk (and I’ve never gotten a speaker gift before), but I’m still pretty confident that this was the best. They gave me a SneakyBook recycled book with a flask inside.
The flask was not only laser etched on the front with the 2016 logo, but it also had my name on the back!
This was an amazing con, and well worth the time/money. I plan on coming to this every year that I can from now on.
BSides Raleigh 2017 was last weekend, and it was another great year.
This was my second year at BSides Raleigh, and I definitely still recommend going.
I was able to attend two talks (counting my own) this year, so that’s more than last year!
The venue was the same as last year, and a lot of the same vendors were there. That said, I convinced Secureworks to sponsor, so we had a booth there as well.
I was able to attend An Introduction to Reverse Engineering with Binary Ninja by psifertex the day before the con.
This was a great course, and an even better reason for me to finally pick up a license.
I had never used Binary Ninja before, and Jordan did a great job balancing the introduction to the tool/RE in general. That said, I think this course could be even better if it was 2 days long.
I do have some ideas for uses now though, and I still want to finish up (and blog about) the bomb lab!
Cliff Stoll gave the keynote this year, and it was a talk to catch.
If you’ve never read it, then I highly recommend The Cuckoo’s Egg. This is the book he is most known for, and what a lot of his keynote was about.
I wish that the organizers could post his talk online, but he asked them not to.
That said, it was a riveting talk with topics ranging from his book to physics, and even to modern-day security/cellphones.
I’ve heard that it is very similar to his TED Talk, which I need to check out.
I was finally able to give my talk this year, albeit slightly modified.
We originally submitted our talk from CarolinaCon, “CTFs – Not Just for Halo”. That said, Jordan also submitted an awesome sounding talk about CTFs.
After talking with the organizers, we decided to combine both talks into one panel.
It was great being up there with Jordan, and most of EverSec was able to join in as well.
The crowd asked plenty of great questions about running and competing in CTF and gave us lots of ideas. Additionally, we were able to interject with some stories and ideas of our own.
Hopefully, this motivated even more people to run or take part in CTFs.
The video is not posted yet, but I’ll be sure to share it once it is.
While I wasn’t competing this year, I spent most of my time in the CTF area.
The CTF was again run by EverSec, and it was another good one. Some of the challenges were similar to last year’s, but there were a lot of new ones.
I helped everyone run it where necessary (though Gabe does most of this work), and gave out a few hints here and there.
The EverSec CTF operates in a mixed/scenario format, similarly to the DerbyCon CTF. A company got “hacked” and needed help finding out additional information for them.
That said, I ended up trying a few challenges to test them out and for future write-ups. Doing so, I accidentally ended up in fourth place.
I didn’t accept any prize though, so my choice went to 5th place, etc.
The challenges that I did complete were pretty fun though, so stay tuned for the write-ups.
First, I performed some NodeJS command injection and got a reverse shell from one of their systems.
Next, I solved an interesting crypto challenge that was giving other people some trouble.
Finally, I was able to hijack two of EverSec’s subdomains and post my Russian propaganda on them.
Towards the end of the CTF, Veracode ran another round of Hacker Jeopardy.
I didn’t compete in this either, partly because of how much I won last year, and partly to mess with Patrick. Even though I didn’t compete, I managed to win a nice windbreaker from the business card drawing beforehand.
Another year, and another super awesome speaker gift! I again received a SneakyBook recycled book with a flask inside. They forgot I had already received one last year, but I was still glad to receive another.
Just like last year, the flask was laser etched with the 2017 logo on the front, and my name on the back!
Another awesome local con, and I cannot wait until next year.
If you have a talk idea? Submit it! If you have a company? Convince them to sponsor! If you’ve never been to a con before? Come to this one!
I’m already working on my talk idea for next year, and even some new CTF challenges.
Get Your NordVPN Offer Now!I know it’s a little late, but I finally finished up my BSidesRDU 2018 post!
For those of you who don’t get a title, it is a Bon Jovi reference, this is the same conference that was BSides Raleigh. The organizers changed the name for inclusion, plus because the venue was in Durham this year.
This was another great conference, complain as I might about having to go all the way to Durham. That said, this was the first one that I attended and didn’t speak at.
It was another good year, and I recommend checking it out if you are in or near the Triangle.
The new Twitter account is here, if you’d like to follow them for pictures and updates! Also, here is the new website for the conference.
Unfortunately, I was only able to catch part of the, “Movement After Initial Compromise – SleepZ3R0 and HA12TL3Y” talk, and that was it this year.
That said, Adrian already has the videos up on YouTube, so you can catch up along with me!
This was the second con in a row that I helped with booth duties, which was great.
SwAG was a Gold-level sponsor and managed to have the booth right by the entrance.
I didn’t spend a ton of time at the booth, but it was very similar to Derby. We had a few more people solve our Crypto challenge, which was great.
Other than that, it was another opportunity for potential sales or recruiting, which helps.
The CTF is where I spent almost all of my time this year, and it went great. We (EverSec) had the privilege of hosting again this year, and it was fun.
While I don’t have too many pictures of the room, here is one of Steve holding down the fort.
There were no server fires at this con, which was great.
I made a nice mess of things when they gave me all the venue’s gaffer tape during our setup. That said, I’m hoping that I can convince the con or Gabe to get me a GaffGun for next year!
I wasn’t competing again this year, but I was around for write-ups and general help/support. I already finished my write-up using zsteg, but I’ve got about 4 more on the way.
In the end, it was a great competition, and Welcome Thrillhouse Group took first place!
You can find some of their write-ups here, so be sure to take a look.
If you have any suggestions for the CTF or want to submit some challenges, then definitely reach out to me!
I took part in Hacker Jeopardy again this year. That said, I might get banned again/on hiatus next year after my performance.
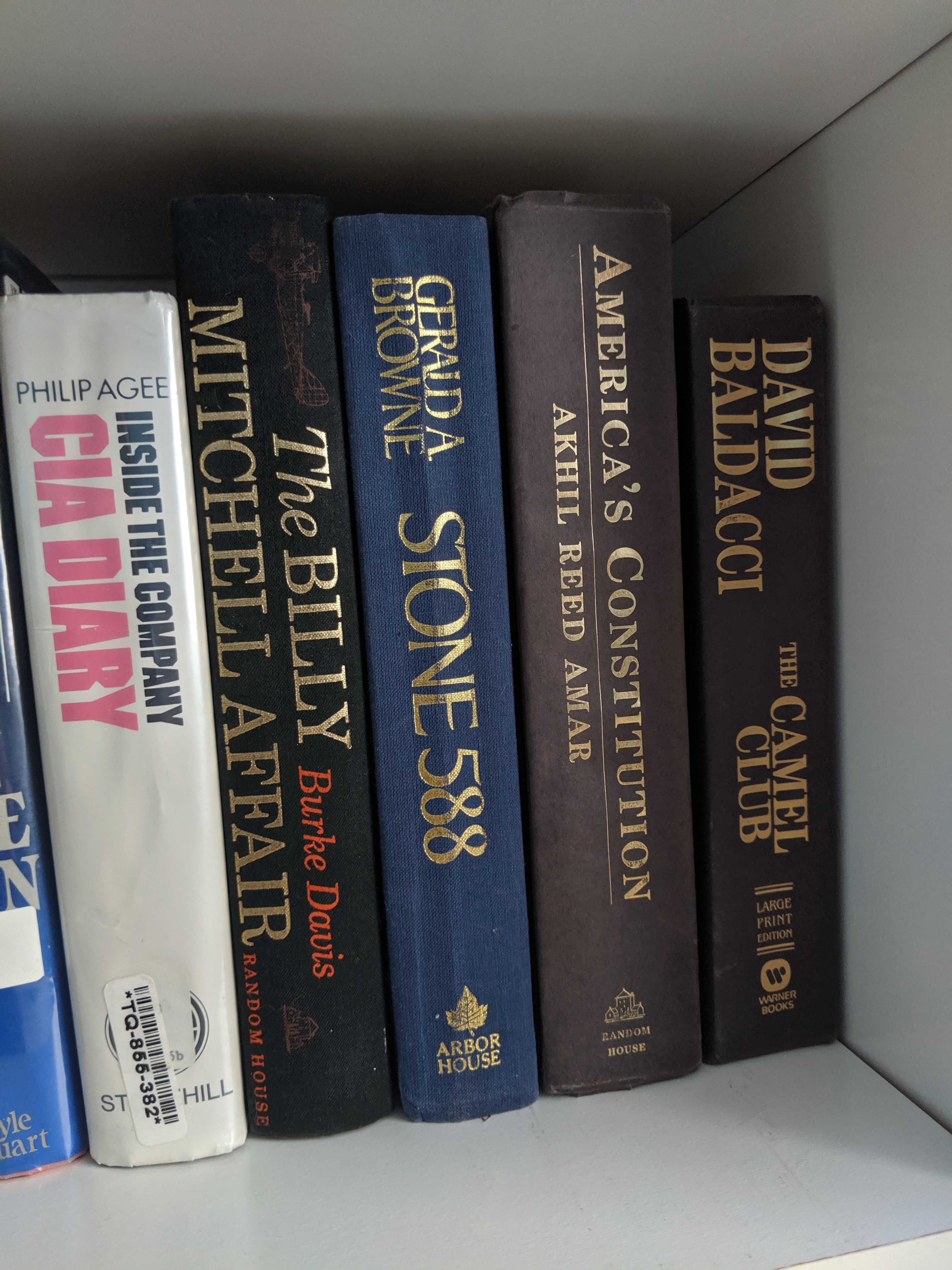
I killed it again this year at Hacker Jeopardy, but big thanks to Patrick for running it. The final score was 180-0-0, and I ended up winning $60 in Amazon gift cards and a 3rd @BSidesRDU flask book for my collection!
Other than that, I was also able to buy a Crazyradio in the silent auction with my winnings. I’ve had one of these in my Amazon wish list for a little while, so be on the lookout for a post/talk about my new toy.
The flask was awesome again, although this one doesn’t have my name on it this year.
Hacker Jeopardy was tons of fun and a solid reminder that I’m pretty decent at trivia and the like.
Another awesome local con, and I cannot wait until next year. That said, I’ll probably keep complaining about having to drive to Durham.
I’m hoping to speak again next year, but I’ll have to figure out what to speak about. Other than that, hopefully, I can finish some CTF challenges in time as well.
At this rate, I’m going to need a new bookshelf just for my BSidesRDU collection though.
Yesterday (18 October 2019) was BSidesRDU 2019, so it’s time for another conference blog post!
This was officially the second year of BSidesRDU, as the earlier iterations were BSides Raleigh.
The theme this year was Security Dumpster Fire, and it turned out awesome. There was even this sweet badge to go with the theme.
For another review, you can check out Steve’s post.
Chris Wysopal (WeldPond) gave the keynote address this year, and the topic was, “Security is already here - it's just not evenly distributed yet”.
I wish I could summarize this talk better, but I couldn’t do it justice. Instead, I’ll just give you the description from the website/pamplet:
“When the FBI is having a hissy fit because Apple can't help them unlock the data on a phone you know it is pretty secure. On the other hand, there are products shipping without signed updates and people still manage to make their S3 bucket world-readable. The knowledge to build and operate secure systems is out there. Why don't we implement it? This talk will take a look at how to distribute security more evenly across all technology.”
I highly recommend watching this talk once the videos are posted.
I spoke again this year, and it went well.
For starters, I made a “special request” as a speaker, and Patrick came through for me! Of course, I shared them with whoever asked, but it was still a fun time.
My topic was, “What is HTTPS, and Why Does It Matter?”, and I had to go on stage right after the keynote!
This was the only conference that accepted this talk this year, so I’m glad that I got the opportunity to present it.
I’ll have the slides (and videos) up soon, but please let me know if you have any questions or comments in the meantime.
Special shout-out to Rebecca for paying attention to my slides!
The only other talk that I made it to this year was Rebecca’s, “Extinguishing the Vulnerability Management Dumpster Fire”. This was another good one that was both fun and informative. I also recommend checking it out once BSidesRDU posts the videos.
I spent a little time helping at our booth, but I wasn’t officially scheduled to spend any time there.
That said, a few of my co-workers held it down, and rocked our orange.
I also made sure to harass and catch up with Michael and the rest of the SwAG crew that came out.
Another BSides, and another CTF by EverSec CTF.
This year went well, and even better with the gear we got from the DerbyCon crew!
We had over 50 participants/teams, and there were only a few issues, but no actual server fires again!
I also wanted to thank strupo, and anyone else that helped at the CTF noobs table.
The prizes this year were awesome, and I wanted to thank everyone who donated them or time.
From eLearnSecurity, we got an eCPPT voucher and eJPT voucher, which went to 1st and 3rd place respectively.
We also got a SANS NetWars voucher, which went to 2nd place.
Finally, we got an AWESOME trophy, made by the amazing JoyKil.
Also, if you did not see her leggings, then you really missed out!
In the end, Cos1ne ended up on top, with a decent lead.
I’ve got at least one, if not more, write-ups for challenges that I wrote or solved. In the meantime, I recommend you check-out Steve’s write-ups for the challenges that he created.
Just like 2017 and 2016, I got a special speaker’s gift from the crew!
This was another sneaky book, which was is so cool.
The conference logo for this year was laser etched on the front.
And, like before, my name was etched onto the back!
There was also a speaker dinner the night before at Blue Corn Cafe. This was a fun time, and I had some pretty awesome food.
This is one of the best conferences for speakers, and you feel appreciated when you give a talk here.
There was no hacker Jeopardy this year, but that is my only complaint (other than location).
If you live anywhere near the Triangle, then I highly recommend that you head to this con next year.
Not sure what my topic for next year will be, but I’ve already got ideas for new CTF challenges.
Finally, my bookshelf is getting fuller year by year!
Get Your NordVPN Offer Now!Unfortunately, BSidesRDU had to be canceled for 2020 due to the pandemic.
That said, it was nice to take a year off, and I’m looking forward to seeing everyone in 2021 or 2022!
I’m so glad that I’ve been to this conference for four of the last five years, and I HIGHLY recommend it to anyone in or around North Carolina.
I’m also wondering when I’ll need to get an entire bookshelf for all of these flasks that I keep getting.
If you have any suggestions for the CTF or events in general, then I’d love to hear them.
Ray Doyle is an avid pentester/security enthusiast/beer connoisseur who has worked in IT for almost 16 years now. From building machines and the software on them, to breaking into them and tearing it all down; he’s done it all. To show for it, he has obtained an OSCE, OSCP, eCPPT, GXPN, eWPT, eWPTX, SLAE, eMAPT, Security+, ICAgile CP, ITIL v3 Foundation, and even a sabermetrics certification!
He currently serves as a Senior Staff Adversarial Engineer for Avalara, and his previous position was a Principal Penetration Testing Consultant for Secureworks.
This page contains links to products that I may receive compensation from at no additional cost to you. View my Affiliate Disclosure page here. As an Amazon Associate, I earn from qualifying purchases.
[…] the BSidesRDU CTF, there was a challenge to reverse Electron […]
[…] covered this in my talk at BSidesRDU 2019, and I’ll hopefully be sharing the slides/video for that […]
[…] the BSides RDU 2018 CTF, I of course found a login […]
[…] only cons left on my docket for 2018 are DerbyCon and BSidesRDU, so it’s time for the closing […]
[…] Best Hacker Conference in the Area? BSidesRDU! […]
[…] Best Hacker Conference in the Area? BSidesRDU! […]
[…] Best Hacker Conference in the Area? BSidesRDU! […]
[…] Best Hacker Conference in the Area? BSidesRDU! […]
[…] I love DEF CON and BSides RDU, DerbyCon hit that sweet spot right in the […]
[…] Best Hacker Conference in the Area? BSidesRDU! […]