Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
If you want to perform a pfSense speed test from the command line or your web UI, then this is the post for you!
I finally reconnected my Zotac pfSense device to my new network, and I wanted a way to check the upload and download speeds.
The speedtest-cli tool seemed perfect for this, and there was already a FreeBSD package.
As an added benefit, I found a few issues with my firewall, so I’m glad that I installed this too.
First, I updated my local package catalogues before installing the tool.
[2.4.5-RELEASE][[email protected]]/root: pkg update Updating pfSense-core repository catalogue... pfSense-core repository is up to date. Updating pfSense repository catalogue... pfSense repository is up to date. All repositories are up to date.
Next, I installed the speedtest-cli tool.
[2.4.5-RELEASE][[email protected]]/root: pkg install -y py37-speedtest-cli Updating pfSense-core repository catalogue... pfSense-core repository is up to date. Updating pfSense repository catalogue... pfSense repository is up to date. All repositories are up to date. The following 1 package(s) will be affected (of 0 checked): New packages to be INSTALLED: py37-speedtest-cli: 2.1.1 [pfSense] Number of packages to be installed: 1 37 KiB to be downloaded. [1/1] Fetching py37-speedtest-cli-2.1.1.txz: 100% 37 KiB 37.7kB/s 00:01 Checking integrity... done (0 conflicting) [1/1] Installing py37-speedtest-cli-2.1.1... [1/1] Extracting py37-speedtest-cli-2.1.1: 100%
With the tool installed, I just needed to run the ‘speedtest-cli’ command, and it tested my speeds for me.
[2.4.5-RELEASE][[email protected]]/root: speedtest-cli Retrieving speedtest.net configuration... Testing from AT&T... Retrieving speedtest.net server list... Selecting best server based on ping... Hosted by AT&T [7.88 km]: 17.273 ms Testing download speed................................................................................ Download: 477.22 Mbit/s Testing upload speed...................................................................................................... Upload: 28.79 Mbit/s
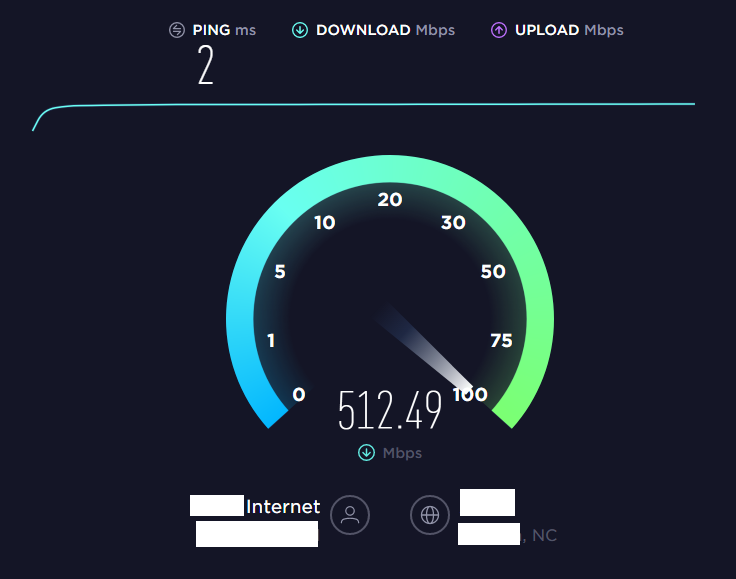
As you can see, this download speed lined up with the actual SPEEDTEST web interface.
Unfortunately, my upload speed was nowhere near expected (1gbps).
That said, when I tried the web interface, I was receiving an error and unable to complete the upload part.
After some research, it seemed that I should expect the slower download speeds.
As you can see, my CPU was spiking when I was running any intensive traffic.
As it turns out, the upload failure was due to the Realtek NICs in my firewall. After installing the updated drivers, I reran the test.
As you can see, while I was still not getting full gigabit, the upload was succeeding at a reasonable speed.
[2.4.5-RELEASE][[email protected]]/root: speedtest-cli Retrieving speedtest.net configuration... Testing from AT&T... Retrieving speedtest.net server list... Selecting best server based on ping... Hosted by AT&T [7.88 km]: 12.618 ms Testing download speed................................................................................ Download: 534.40 Mbit/s Testing upload speed...................................................................................................... Upload: 376.16 Mbit/s
While this was a simpler tool, it was nice to easily check my speeds from the command line.
For an example of running a scheduled task from the pfSense UI, I recommend this blog post.
Unfortunately, all this testing showed that my tried and true Zotac box was getting a little long in the tooth.
That said, I’ve got a planned upgrade on the way, so stay tuned for those specs and review!
Ray Doyle is an avid pentester/security enthusiast/beer connoisseur who has worked in IT for almost 16 years now. From building machines and the software on them, to breaking into them and tearing it all down; he’s done it all. To show for it, he has obtained an OSCE, OSCP, eCPPT, GXPN, eWPT, eWPTX, SLAE, eMAPT, Security+, ICAgile CP, ITIL v3 Foundation, and even a sabermetrics certification!
He currently serves as a Senior Staff Adversarial Engineer for Avalara, and his previous position was a Principal Penetration Testing Consultant for Secureworks.
This page contains links to products that I may receive compensation from at no additional cost to you. View my Affiliate Disclosure page here. As an Amazon Associate, I earn from qualifying purchases.