Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
I started using Gimme AWS Creds recently, and it has been a lifesaver.
If you are not familiar, gimmie-aws-creds is, “A CLI that utilizes Okta IdP via SAML to acquire temporary AWS credentials.”
You can find Nike’s GitHub repository here.
While I did not use this during my NPK installation, our AWS policies have changed since them.
As I now need to use my personal AWS account, I needed a way to programmatically grab an access and secret key for my 2FA protected account.
Get Your NordVPN Offer Now!First, I installed the AWS CLI, as this is necessary for the AWS interaction.
ubuntu@awshost:~$ sudo apt-get install awscli
Next, I used pip to install the gimme-aws-creds module. Note that I was missing the keyrings.alt package and had to install it manually.
ubuntu@awshost:~$ pip3 install --upgrade gimme-aws-creds Collecting gimme-aws-creds ... ubuntu@awshost:~$ pip3 install --upgrade keyrings.alt
Once I had everything installed, I ran the application with the configure flag.
ubuntu@awshost:~$ /home/ubuntu/.local/bin/gimme-aws-creds --action-configure If you'd like to assign the Okta configuration to a specific profile instead of to the default profile, specify the name of the profile. This is optional. Okta Configuration Profile Name [DEFAULT]: Enter the Okta URL for your organization. This is https://something.okta[preview].com Okta URL for your organization [https://redacted.okta.com]: Enter the URL for the gimme-creds-server or 'internal' for handling Okta APIs locally. URL for gimme-creds-server [internal]: appurl Enter the application link. This is https://something.okta[preview].com/home/amazon_aws//something Application url: https://redacted.okta.com/home/amazon_aws/0o...d8/272?fromHome=true Do you want to write the temporary AWS to ~/.aws/credentials? If no, the credentials will be written to stdout. Please answer y or n. Write AWS Credentials [y]: Do you want to resolve aws account id to aws alias ? Please answer y or n. Resolve AWS alias [n]: Do you want to include full role path to the role name in AWS credential profile name? Please answer y or n. Include Path [n]: Enter the ARN for the AWS role you want credentials for. 'all' will retrieve all roles. This is optional, you can select the role when you run the CLI. AWS Role ARN [all]: If you'd like to set your okta username in the config file, specify the username .This is optional. Okta User Name [doyler]: If you'd like to set the default session duration, specify it (in seconds). This is optional. AWS Default Session Duration [28800]: If you'd like to set a preferred device type to use for MFA, enter it here. This is optional. valid devices types:[sms, call, push, token, token:software:totp] Preferred MFA Device Type [token:software:totp]: Do you want the MFA device be remembered? Please answer y or n. Remember device [n]: Set the tools' output format:[bash, json] Preferred output format [json]: The AWS credential profile defines which profile is used to store the temp AWS creds. If set to 'role' then a new profile will be created matching the role name assumed by the user. If set to 'acc-role' then a new profile will be created matching the role name assumed by the user, but prefixed with account number to avoid collisions. If set to 'default' then the temp creds will be stored in the default profile If set to any other value, the name of the profile will match that value. AWS Credential Profile [default]:
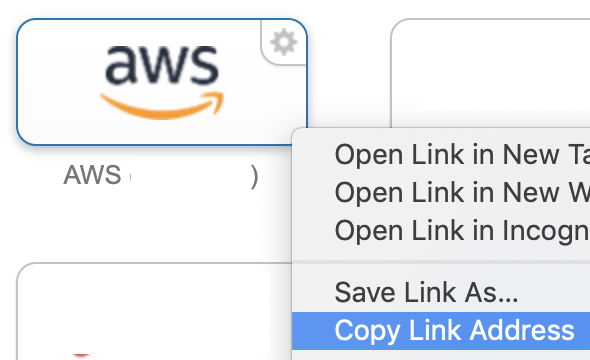
To get the application link, I logged into my Okta portal, and copied the link for my AWS SSO button.
Unfortunately, when I tried to get my credentials, I was getting 403 errors.
ubuntu@awshost:~$ /home/ubuntu/.local/bin/gimme-aws-creds Using password from keyring for doyler Okta Password for doyler: Do you want to save this password in the keyring? (y/n) n Multi-factor Authentication required. token:software:totp( GOOGLE ) : doyler selected Enter verification code: xxxxxx Multi-factor Authentication required. token:software:totp( GOOGLE ) : doyler selected Enter verification code: xxxxxx Traceback (most recent call last): File "/home/ubuntu/.local/bin/gimme-aws-creds", line 17, inGet Your NordVPN Offer Now!GimmeAWSCreds().run() ... <snip> ... File "/home/ubuntu/.local/lib/python3.6/site-packages/requests/models.py", line 941, in raise_for_status raise HTTPError(http_error_msg, response=self) requests.exceptions.HTTPError: 403 Client Error: Forbidden for url: https://redacted.okta.com/api/v1/authn/factors/.../verify?rememberDevice=True
After talking to some of my coworkers, I realized that I needed to register my device. Even though I already linked my Google Authenticator to the account, gimmie-aws-creds needed the registration as well.
ubuntu@awshost:~$ /home/ubuntu/.local/bin/gimme-aws-creds --register_device --profile DEFAULT Using password from keyring for doyler Okta Password for doyler: Do you want to save this password in the keyring? (y/n) Multi-factor Authentication required. token:software:totp( GOOGLE ) : doyler selected Enter verification code: xxxxxx Device token saved!
Note: I also removed the ‘?fromHome=true’ from the application URL, just to be safe.
Finally, after making these changes, I was able to successfully obtain a working .aws/credentials file!
ubuntu@awshost:~$ /home/ubuntu/.local/bin/gimme-aws-creds Using password from keyring for doyler Okta Password for doyler: Do you want to save this password in the keyring? (y/n) n Multi-factor Authentication required. token:software:totp( GOOGLE ) : doyler selected Enter verification code: xxxxxx The requested session duration was too long for this role. Falling back to 1 hour. Saving arn:aws:iam::79xx9:role/myrolehere as default Written profile default to /home/ubuntu/.aws/credentials
Unfortunately, it looks like my 8-hour duration was too long, and Okta kicked me back down to 1 hour.
In the end, my working profile looked like the following:
ubuntu@awshost:~$ /home/ubuntu/.local/bin/gimme-aws-creds --action-list-profiles [DEFAULT] okta_org_url = https://redacted.okta.com okta_auth_server = client_id = gimme_creds_server = appurl aws_appname = aws_rolename = all write_aws_creds = True cred_profile = default okta_username = doyler app_url = https://redacted.okta.com/home/amazon_aws/0o...d8/272 resolve_aws_alias = False include_path = False preferred_mfa_type = token:software:totp remember_device = False aws_default_duration = 28800 device_token = output_format = json
While this was a simpler tool to setup and use, I think that I’ll be using it more in the future.
Stay tuned for another post on AWS password cracking, as I’ve tried out a few more options.
In the meantime, please let me know if you have any suggestions for tools or services.
Ray Doyle is an avid pentester/security enthusiast/beer connoisseur who has worked in IT for almost 16 years now. From building machines and the software on them, to breaking into them and tearing it all down; he’s done it all. To show for it, he has obtained an OSCE, OSCP, eCPPT, GXPN, eWPT, eWPTX, SLAE, eMAPT, Security+, ICAgile CP, ITIL v3 Foundation, and even a sabermetrics certification!
He currently serves as a Senior Staff Adversarial Engineer for Avalara, and his previous position was a Principal Penetration Testing Consultant for Secureworks.
This page contains links to products that I may receive compensation from at no additional cost to you. View my Affiliate Disclosure page here. As an Amazon Associate, I earn from qualifying purchases.